|
T. Andrew Yang
|
last updated: 1/28/2012 |
|||
|
CSCI 5233 Computer Security&
Integrity 1.1 (10 pts)
Visit the class discussion group (link available in the syllabus page). Post
a message with your full name as the subject line. In your post, briefly
introduce yourself (including your full name) and one item you most desire to
learn in this class. Throughout this class, you shall regularly participate
at the discussion group to find recent announcements, reminders, and
discussions.
1.2 Java Cryptography Review information in
the file “Installation
of JCE security provider for unlimited strength security”, and
become familiar with JCE security providers and the unlimited strength Java
security policy. Please note that the instructions given in the document have
been rigorously tested and, if followed correctly, should enable your Java
environment to run all the sample programs that come with the 'Java Security'
book. If you run into problems, double check and make sure you have correctly
completed the required steps. Note:
Sample programs from the book are available on line at http://sce.uhcl.edu/yang/teaching/proJavaSecurityCode.html.
A zip file is available at the top of
that page for you to download all the sample programs. After you have properly
configured your Java environment, perform the following tasks: 1) (15 pts) Test the FileEncryptor.java
program (from chapter 4 of the Garms and Somerfield book). Add a
printline statement at the beginning of the program to print your name as
part of the program’s output. Run the program using sample data of your
choice. Note: Replace all
occurrences of the cipher ‘PBEWithSHAAndTwofish’
with ‘PBEWithMD5AndDES’
in the source program. Hand in the revised
source program and the screen output from the program. 2) (continued from a above, 15%) Give the TA a demo during his office
hours before the due date. 3) (15 pts) Test the FileEncryptorRSA.java
program (from chapter 5 of the Garms and Somerfield book). Add a
printline statement at the beginning of the program to print your name as
part of the program’s output. Run the program using sample data of your
choice. Note: Replace all
occurrences of the cipher ‘PBEWithSHAAndTwofish’
with ‘PBEWithMD5AndDES’
in the source program. Hand in the revised
source program and the screen output from the program. 4) (continued from c above, 15%) Give the TA a demo during his office
hours before the due date. 1.3
The following questions are based on
chapter-end exercises from the textbook. 5) (10 pts) Exercise 1, Chapter 1 (page 25). Justify your answer. (That is,
explain why your answer is correct.) 6) (10 pts) Exercise 2, Chapter 1 (pp. 25-26). Justify your answer. 7) (10 pts) Exercise 3, Chapter 2 (p.45). Go to the Index 2.1 Study the textbooks and/or applicable web sites to find answers
for the following questions. Online glossaries may also be used. Note: Clearly identify the source(s) of your information. 1)
(5 pts) What is a ‘man-in-the-middle attack’? 2)
(5 pts) What is a ‘replay attack’? 3)
(5 pts) Is a replay attack a type of man-in-the-middle
attack? Justify your answer. 4)
(5 pts) What is a ‘session hijacking attack’?
When applicable, show the protocol or draw a diagram to illustrate the
attack. 2.2 Programming project 5)
Description: All
the programming projects for this class involve client/server communications using
sockets. The purpose of this project is for you to become familiar with Java
Sockets programming by running a sample application. 6)
Requirements: Run
the KeyAgreement application in
Chapter 5 of the Java Security book. The application consists of two Java
programs (KeyAgreementClient.java and KeyAgreementServer.java). 7)
Compile and run both
programs (as two separate processes). 8)
In your demo, show the
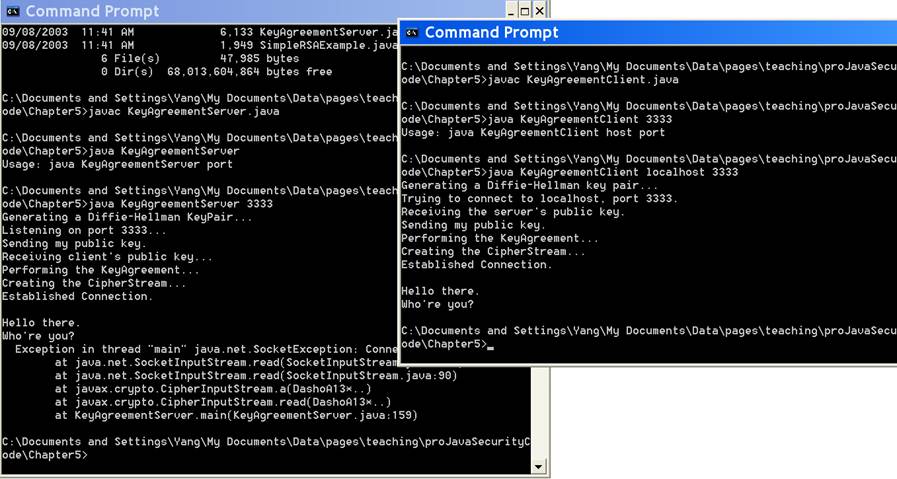
TA how those programs interact with each other. Figure 1 shows a sample
execution of the programs.
Figure 1. Demo of the
KeyAgreeement application (original) 9)
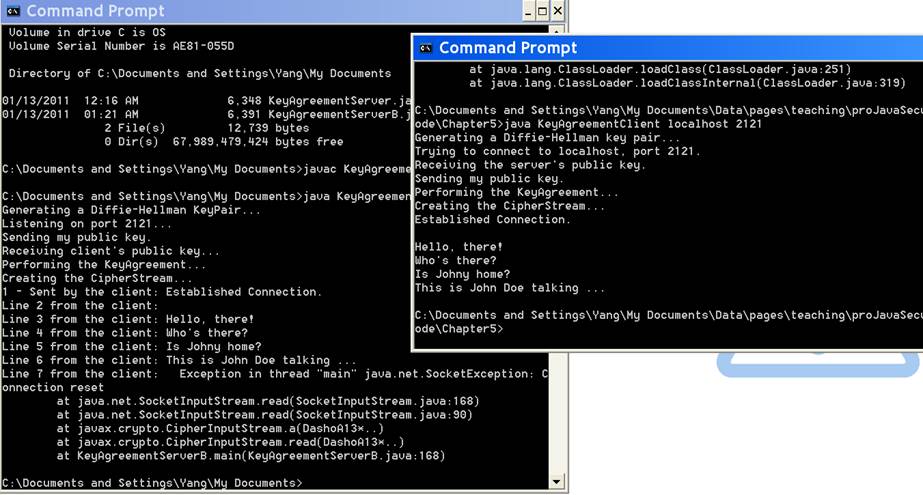
Revise the
KeyAgreementServer.java program, so each time the server program receives a
NewLine character sent from the client, it will display a message like
‘Line n from the client: <the mesg>‘. See Figure 2 for a
sample screen snapshot of a revised program.
Figure 2. Demo of the
KeyAgreeement application (with revised KeyAgreementServer.java) 10) (40 pts) In your demo, show the TA how those programs interact with
each other. 11) (40 pts) Zip the revised KeyAgreementServer
program and the screen snapshot of running the revised application into a
single zip file. Send the zip file electronically to yang@uhcl.edu, cc'ing the TA. Go to the Index 3.1 (5 pts) Using the Extended Euclidean Algorithm, find x and y
such that 31 x + 11 y = 1. 3.2
On page 252 of the Bishop book, a
variation of man-in-the-middle attack in the context of public key
cryptography is discussed, in which the hacker Eve successfully steals
a session key transmitted from Alice to Bob. Examine the attack
scenario and answer the following questions: 1)
(5
pts) What is the source of the problem? That is, what vulnerability makes the attack
possible? 2)
(5
pts) Explain how the problem may be mitigated? Justify
your answer. 3.3 (5 pts) Exercise 1, Chapter 9 (p.241). 3.4 Programming project 1)
Project description: The
purpose of this project is to build a client/server application which uses
symmetric encryption to exchange a new key. The application will be used as a
base for the later projects. The communication between the client and the
server is to be implemented as sockets. a) The client application will take a plaintext message (m)
from the user, encrypt the message using a TripleDES key (assuming
an existing key, k), and then send the ciphertext over the socket to
the server. NOTE: The key may be generated by the
client program, stored into a file, and then shared with the server program. b) The server will read the ciphertext from the socket, get the
secret key k from the user, and then decrypt the ciphertext. The decrypted
message (dm) should be printed as part of the screen output. c) The server then generates a new TripleDES key
(nk), encrypts dm by using nk, encrypts nk
by using the existing symmetric key (k), and then sends the encrypted
new key and the encrypted dm over to the client. d) Once the client receives the encrypted dm and the
encrypted nk, it first decrypts the encrypted nk to get the new
symmetric key, and then uses the new key to decrypt the encrypted dm.
The outcome from the decryption of dm should be compared against the
original plaintext message (m), which was originally sent over to the
server. Print appropriate message depending on the result of the comparison. 3)
Project Report (to be submitted electronically to yang@uhcl.edu, cc'ing the TA, as a single zip
file) a) (20 pts) Program design
i.
Use UML to define class
diagrams for CLIENT, SERVER, and any other necessary classes. Clearly
identify the attributes and methods defined in each of the
classes, and the associations among the classes.
ii.
For each of the methods,
briefly explain its functionality and clearly indicate its parameters (if
any) and returned data type. b) (35 pts) Source programs and execution results
iii.
A copy of the class
diagram (possibly refined from the preliminary report). If no revisions were
done, simply attach the original UML diagram.
iv.
The source programs
implementing your design.
v.
A readme file
explaining how to compile and run your source programs.
vi.
Test the application by
using three different plaintext messages. For each of the test
cases, attach a screen output showing the following: 1.
the original message
(m), 2.
the ciphertext sent by
the CLIENT (ci), 3.
the decrypted message by
the SERVER (dm), 4.
the ciphertext sent by
the SERVER (cs), 5.
the decrypted message by
the CLIENT (dmc), 6.
The result of the
CLIENT’s comparing m and dmc. c)
(25 pts) Program
demonstration: You are required to
give the TA a demo of your final project during his/her office hours. The
demo shall be completed before the project due date. The demo
constitutes 30% of the project’s total grade. Go to the Index 4.1 (10 pts) Exercise 2, Chapter 9 (p.241).
Explain your approach. 4.2 (10 pts) Exercise 6, Chapter 9 (p.241) 4.3 (50 pts) Exercise 8, Chapter 9 (p.242). Show
all the intermediate steps. 4.4 Exercise 17, Chapter 9 (p.243) 4.4.1
(10 pts) The explanation 4.4.2
(10 pts) The modified
protocol 4.5 (10 pts) Exercise 2, Chapter 10 (p.273) Go to the Index 5.1 The questions below are
based on the ‘signature chain' discussion on page 258 of the Bishop
book. Suppose that X<<Y>> represents the certificate that X
generated for the subject Y (X is the CA that issued the certificate). It is
assumed that a subject always has the public key of its root CA, but not
necessarily its immediate CA. a)
(5
pts) Suppose Y has generated a certificate for
Z. How does Z’s certificate look like? b)
(5
pts) (Continued from above) When Z sends its
certificate to another entity R, how would R verify that certificate? Explain
in detailed steps how the verification would work. Assumption: The only trusted
public key that R has is X’s public key. c)
(10
pts) Suppose P’s certificate is created
by O, and Q’s certificate is created by P. The only trusted public
key that Q possesses is O’s public key. Show how cross-certification
may be implemented between X and O such that, when Q receives Z’s
certificate, Q will be able to verify that certificate. d)
(10
pts) (Continued from above) Show in detailed
steps how Q would verify Z’s certificate (when cross-certification
between X and O is in place). 5.2 Programming project 1)
Project description: The
purpose of this project is to create multi-level certificate paths (aka. certificate
chains), and use a sample program to verify the certificate paths. 2)
Requirements: a) Perform the following tasks to familiarize yourself with the
basic tools and information with respect to multi-level certificate chaining. b) Refer to http://java.sun.com/javase/6/docs/technotes/tools/windows/keytool.html
to learn how to use keytool to
create self-signed certificates. c)
Study the sample
program, SignCertificate.java, which can be used to allow one entity
to sign the certificate of another entity. The program is discussed in
Chapter 6 of the Garms and Somerfield book; see http://sce.cl.uh.edu/yang/teaching/proJavaSecurityCode/Chapter6/SignCertificate.java
for the source codes. d)
A
document explaining how to create multi-level certificate paths is
available as Creating
Certificate Chain.doc. Practice the examples in that document to learn
how to create multi-level certificate paths. e) Use keytool to create the following certificate chains. Use proper names and relevant information for each of them. f)
Create the certificates
of the following certifying authorities: rootCA, CA1, and CA2. CA1 and
CA2 are certified by rootCA. g) Create certificates for the Server and the Client
applications. The Server (S) is certified by CA1; the Client
(C) is certified by CA2. h) Use RSA when generating the key pairs for the server, the
client, and the CAs. i)
(40 pts) Show the commands you have
issued to create the certificates for the Server
and the Client, and the screen snapshots showing the
content of the certificate paths for Server
and Client, which you created
in step 7 above. (This part should be submitted
electronically to yang@uhcl.edu,
cc'ing the TA, as a single zip file.) j)
To learn how to process
multi-level certificate paths in your Java
programs, unzip and run this sample application. k) (30 pts) Give the TA a demo during his/her office hours to show that
you are able to run the sample application in step 9 above. The demo
shall be completed before the project’s due date. Go to the Index 6.1 Programming project 1)
Project description The
goal of this project is to extend the FileEncryptorRSA
program (pages 98-110 of the Garms book) into a two-user application,
incorporating certificates and digital signatures. 2)
Requirements 3) Certificate Chaining: Use
keytool to create the certificates of four certifying authorities,
including rootCA, CA1, CA2, and CA22. Use proper names and relevant
information for them. Also create certificates for the server and the client
applications. Use RSA when generating the key pairs for the server (S),
the client (C), and all the CAs. a) The server is certified by CA1. b) The client is certified by CA22, which is
certified by CA2. c) Both CA1 and CA2 are certified by rootCA;
rootCA’s certificate is self-signed. 4)
The Server (i.e., the encryptor/sender) a)
The server’s certificate should be signed by its CA, as
specified above (certificate chaining). Then, the server can either send its
certificate to the client or save it in a keystore, which is then shared with
the client. b) The server should get the
client’s public key from the client’s certificate. c) The server needs to verify the client’s certificate. d) If the verification succeeds, the server retrieves the client’s public key from
the certificate. Otherwise, an appropriate error message should be displayed.
e) The server should generate a 256-bit Blowfish session key (sk), which is to be used to
encrypt a data file. Use this sample data file
when testing your program. f) For the purpose of data and origin integrity, the server will
generate a digital signature (ds) based
on the content of the data file. That is, the content of the data file is
the message used by the server to generate the digital signature. g)
The session key itself (sk) will be encrypted by the
client’s public key (for confidentiality), resulting in an encrypted session key (esk). h) The encrypted session
key (esk), the digital signature
(ds), and the encrypted data file
(edf) are then sent to the client. 5) The Client (i.e., the
decryptor/receiver) a)
The client’s certificate should be signed by its CA, as
specified above (certificate chaining). Then, the client can either send its
certificate to the server or save it in a keystore, which is then shared with
the server. b) The client should get the server’s certificate and
verify it. c) If the verification succeeds, the client retrieves the server’s public key from
the certificate. Otherwise, it displays an appropriate error message. d) Once receiving the data sent from the server (step 8 above),
the client should first extract the encrypted
session key (esk), the digital
signature (ds), and the encrypted
data file (edf). e) The client then uses its own private key to decrypt the encrypted session key (esk). The
extracted session key (sk2) should
be examined for its integrity, by using the attached MAC. f) If the data integrity of sk2
is not verified, the client should print an appropriate error message;
otherwise, it uses sk2 to decrypt
the encrypted data file. g) The client then verifies the digital signature (ds) using the
server’s public key and the content of the data file. h) If the verification succeeds, the client will display the
content of the file on the screen. Otherwise, it prints an appropriate error
message. 6) Testing Cases: Arrange three test cases as outlined
below. Case 1: Generate proper keyPair
respectively for the server and the client. Run the programs so the content
of the file sent by the server is displayed on the client’s screen. Use
the sample data file mentioned above. Case 2: Produce an error in the
generation of the client’s certificate such that the verification
performed by the server would fail. An example of such errors is that the
client’s certificate is not signed by a proper CA. 7)
Project Report (Pack all items listed below into a single zip
file, and then send the zip file electronically to yang@uhcl.edu, cc'ing the TA.) a) (20 pts) Program design
i.
Use UML to define class
diagrams for SENDER, RECEIVER, and any other necessary classes.
ii.
Clearly identify the attributes
and methods defined in each of the classes, and the associations
among the classes.
iii.
For each of the methods,
briefly explain its functionality and clearly indicate its parameters (if
any) and returned data type. b) (10 pts) Security
analysis: Explain what security
features are built into this application. For each of the features,
explain how it is achieved in the application. c)
(40
pts) Source programs and execution results i. The source programs.
ii.
The data file.
iii.
Screen snapshots of
using keytool to create the certificates.
iv.
Screen
snapshots of running the programs (showing certificate verification, MAC
verification, signature verification, data file decryption, etc.) d) (30 pts) Program demonstration: Arrange time to give a demo for showing the testing cases to the TA before the project’s due date. Go to the Index 7.1 (20 pts) Exercise 6, Chapter 10 (p.273). 7.2 (20 pts) Exercise
7, Chapter 10 (p.273). 7.3 (20 pts) Exercise
2a, Chapter 12 (p. 335). 7.4 (20 pts) Exercise
2b, Chapter 12 (p.335). 7.5 (20 pts) Exercise
10a, Chapter 12 (p.336). Go to the Index |
||||